MainTegrity CSF + IBM SGC
The industry’s most complete mainframe cyber resilience solution.

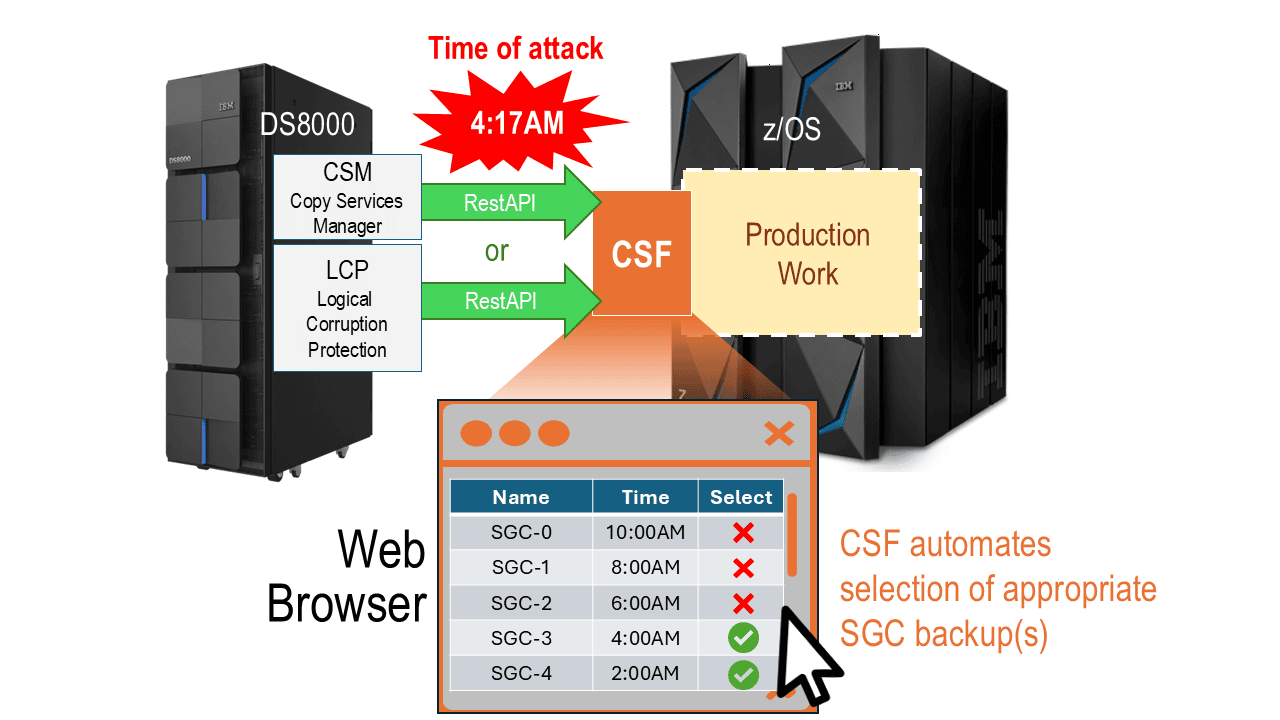
CSF's intelligent browser-based UI
CSF integrates directly with CSM (Copy Storage Manager) or LCP (Logical Corruption Protection) on DS8000 via RestAPI to find and display the list of available SGCs. Since CSF knows the time of attack, it can identify the right SGC to recover your data using existing tools.
Working in tandem, CSF automates the recovery of compromised system software. This ensures both system and data can be returned to their trusted state quickly and precisely.
But, unlike other mainframe products, CSF can:
But, unlike other mainframe products, CSF can:
| Identify and eliminate malware / ransomware | Detect and stop rogue encryptions instantly | Freeze offending actors to mitigate damage and reduce human reaction time |
| Send real-time alerts with automated actions to assist support staff | Dynamic exfiltration intervention – prevent outage / damage | Support recovery from Conventional & Immutable Backups |
| Automate surgical restore of components to the trusted state | Integrate with ServiceNow, Splunk, Rocket, Vertali, IBM, Dell, Hitachi, BMC … | Neutralize insider threats by monitoring suspicious actions |
CSF + SGC
CSF + SGC
| SGC Capability | CSF Enhancement | Combined Benefit |
|---|---|---|
| Whole site backups | Identify what was compromised | Faster, more accurate recovery decisions |
| Immutable | Forensic timeline integration | Know exactly which SGC to use |
| Multiple recovery points | Attack intelligence | Understand when/what must be recovered |
| Comprehensive recovery assets | Links to Copy Services Manager | Know when SGC creation succeeds/fails |
How CSF Amplifies SGC Value
In the rare event that recovery is required, CSF automates the process:
Queries the DS80xx subsystem to generate SGC lists
Displays available copies for instant selection
Provides critical knowledge to enable data restoration with existing tools
Performs automated surgical system restore to trusted state — something z/OS alone cannot do