The Attack Vectors Have Changed
Direct attacks against mainframes are rare. What has replaced them is far more dangerous.
Attackers no longer need 40 years of mainframe experience. They compromise a trusted network device, move laterally into the mainframe, and use valid credentials to walk through the front door. Traditional security tools like RACF, ACF2, and Top Secret can't help when the attacker already has the keys.
The adversary has thousands of well-funded engineers, now augmented by AI. The gap between attack capability and defensive capacity has never been wider.
CSF was built for this reality: assume the perimeter will be breached, then detect what people with legitimate credentials are doing and stop them when behavior turns malicious.
Protect yourself from:
Attacks Are Easier Than You Think
The "nobody understands mainframes" defense is dead. Modern mainframes run Unix System Services, support SSH, expose REST APIs, and execute Python. These are attack surfaces any modern hacker understands.
From real-world penetration testing:
- Privilege escalation (becoming RACF SPECIAL) requires only 6 assembler instructions
- User impersonation (acting as another user) requires only 7 instructions
- AI assistance: ChatGPT generated working mainframe hardware encryption assembler code
- Tools freely available: Pen testing tools on GitHub can be used by attackers
You don't need 40 years of mainframe experience to attack a mainframe. Early Warning levels the playing field.
One pentester went from non-privileged logon to full system control in 6.3 minutes. Freely available tools on GitHub make this repeatable by anyone willing to read the instructions.
The IBMUSER Attack Vector
Every z/OS system has IBMUSER — a high-powered default account. Most sites disable it, but it often remains available in a revoked state. Attackers who gain RACF SPECIAL can:
- Resume the IBMUSER account
- Set their own password
- Log on with superuser capabilities
Early Warning detects successful IBMUSER logons — which should never occur in production.
AI Enabled Threats
The AI Threat Multiplier
AI has fundamentally changed the economics of mainframe attacks. Tools like ChatGPT can generate working mainframe exploit code — assembler, JCL, encryption routines — in seconds.
- AI explains differences between mainframes and other environments to attackers who've never seen oneames and other environments to attackers who've never seen one
- AI enables simultaneous, customized attacks against dozens or thousands of targets
- AI-driven scanners sweep the internet identifying mainframes by open ports (TN3270, SSH, HTTP)
CSF provides the detection speed that AI-assisted attacks demand. When attacks happen at machine speed, your defense must operate at machine speed.
Compromised Network Devices
Most mainframe attacks don't start as mainframe attacks. Threat actors compromise a Windows server, Linux host, or VPN appliance first, then move laterally until they reach the mainframe.
- Compromised Windows, Linux, and Apache servers with trusted mainframe connections
- Partner-owned devices with weaker security postures
- VPN appliances, API gateways, and IoT endpoints on the corporate network
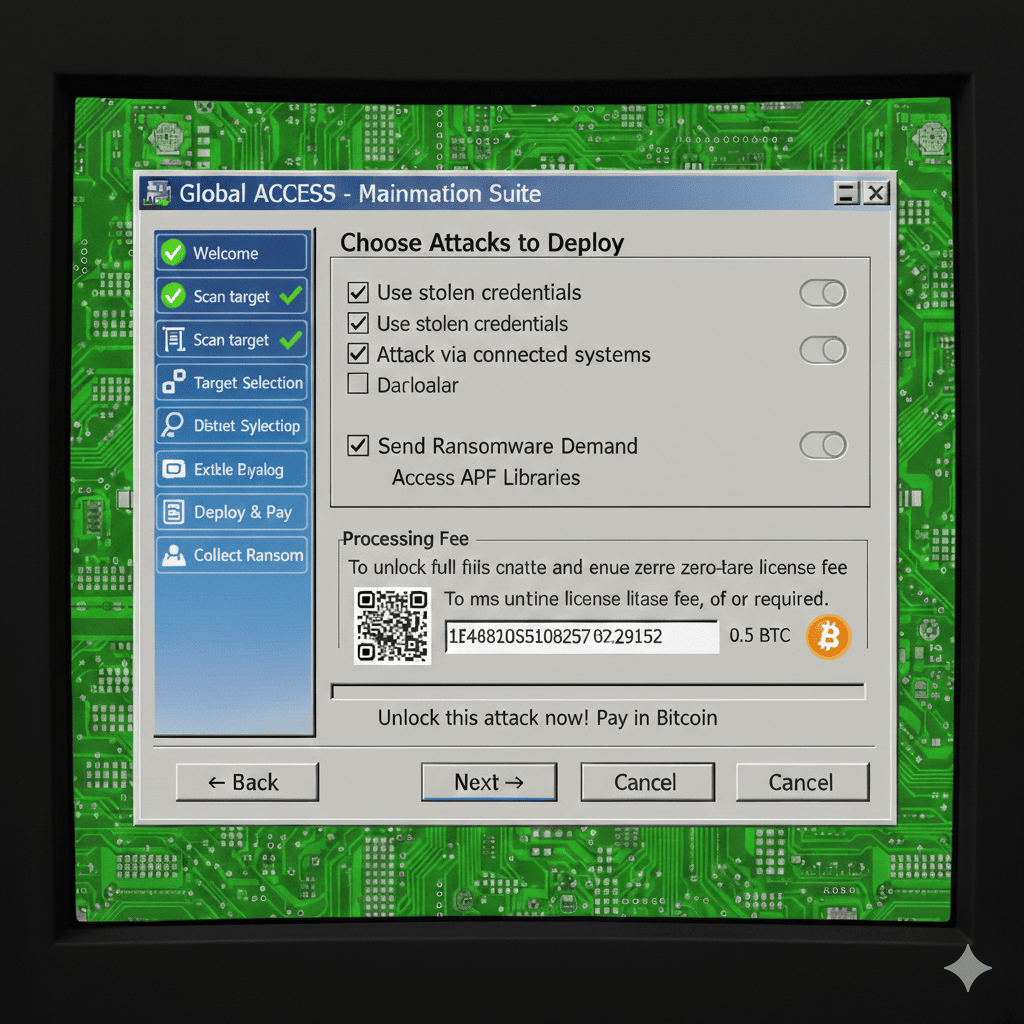
Ransomware as a Service (RaaS)
One-stop shopping for attackers.
Specialized RaaS operations custom-build attack software targeting specific organizations. These aren't amateurs — they're commercial-grade operations, often state-sponsored, with thousands of well-funded engineers now augmented by AI.
- Revenue-sharing model between RaaS providers and attackers
- AI-powered tooling launches thousands of customized attacks simultaneously
- Modern ransomware is multi-pronged: embed malware, install timebombs, establish backdoors, compromise backups, encrypt data, exfiltrate, then demand ransom
A typical mainframe site has 2–4 security staff, often part-time. The gap between attack capability and defensive capacity has never been wider.
Insider Threats
Your biggest threat has a parking spot
Insider attacks use legitimate credentials, making them invisible to perimeter security. A disgruntled system programmer, a compromised partner account, or a stale user ID that was never revoked — all provide the same level of access as legitimate users.
- Stolen or stale credentials bypass every perimeter control
- Privileged users can prepare attacks undetected over days or weeks
- Joiner/mover/leaver failures leave elevated access in place long after roles change
CSF detects insider threats through behavioral monitoring — not credential checking. Early Warning catches reconnaissance and privilege escalation. NetWatch flags abnormal data transfers. FIM+ detects unauthorized file modifications. The credentials may be valid, but the behavior gives them away.
